After a primer on the realities of today’s world, and the totalitarian tendencies that follow from this environment and our behaviour in it, let’s take a look at what this means for professional use of information technology.
Firstly, it should be obvious that when you use the cloud services of a company, you have no secrets from that company other than the ones this company guarantees you to keep. That promise is good up to the level of guarantee that such a company can make due to the legal environment it is situated in and of course subject to the level of trust you can place into the people running and owning the company.
So when using Google Apps for your business, you have no secrets from Google. Same for Office 365 and Microsoft. iCloud and Apple. Also, these companies are known for having very good internal data analytics. Google for instance has been using algorithms to identify employees that are about to leave in order to make them a better offer to keep them on board. Naturally that same algorithm could be used to identify which of your better employees might be susceptible to being head hunted.
Of course no-one will ever know whether that actually took place or whether it contributed to your company losing that important employee to Google. But the simple truth is: In some ways, Google/Microsoft/Apple is likely to know a lot more about your business than you do yourself. That knowledge has value, and it may be tempting to turn that value into shareholder value for either of these businesses.
If you are a US business, or a small, local business elsewhere that may not be an issue.
But if you are into software, or have more than regional reach, it may become a major concern. Because thanks to what we now know about PRISM, your using these services means the US intelligence services also have real-time access to your business and its development. And since FISA explicitly empowers these services to make use of those capabilities for the general interests of the United States – including foreign policy and economic goals – the conclusion is simple: You might just be handing your internal business information to people who are champions for your competition.
Your only protection is your own lack of success. And you might be right, you might be too small for them to use too many resources, because while their input bandwidth is almost unlimited, their output bandwidth for acting upon it of course has limits. But that’s about it.
The US has a long tradition of putting their public services at the disposal of industry, trying to promote their “tax paying home team.” It’s a cultural misunderstanding to assume they would be pulling their punches just because you like to watch Hollywood movies and sympathise with the American Dream.
Which is why the US has been active to promote GM crops in Europe, or uphold the interests of their pharmaceutical industry. Is anyone at Roche reading this? No shareholder is concerned about this? To me it would seem like a good example of what risks are unwittingly taken when you let the CFO manage the IT strategy. Those two professions rarely mix, in my experience.
The United States are not the only nation in the world doing this, of course. Almost every nation has at least a small agency trying to support its own industry in building international business, and the German chancellor typically has a whole entourage of industry representatives when she’s visiting countries that are markets of interests. I guess it’s a tribute to their honesty that the United States made it explicit for its intelligence services to feed into this system in this way.
Several other countries are likely to do the same, but probably not as successfully or aggressively.
Old school on site IT as the solution?
Some people may now feel fairly smart they did not jump on the Public Cloud bandwagon. Only that not all of them are as secure as they think they are. Because we also learned that access to data is not only happening through the public clouds. Some software vendors, most importantly Microsoft, are also supplying the NSA with priority access to vulnerabilities in their software. Likely they will do their best to manage the pipe of disclosure and resolution in a way that there is always at least one way for the NSA to get into your locally installed system in an automated fashion that is currently not publicly known.
This would also explain the ongoing debate about the “NSA back door in Windows” which were always denied, but the denial could have been carefully concealing this alternative way of achieving the same effect. So running your local installation of Windows is likely a little better for your business secrets than using public cloud services by US businesses, but not as much as you might want to believe. But it’s not just Windows, of course, Lotus has been called out on the same practice a long time ago, and one may wonder whether the other software vendors avoided doing it, or simply avoided being caught.
Given the discussions among three-letter agencies about wanting that level of access into any software and service originating in the United States, and provided the evident lack of public disclosure in this area, a rather large question mark remains. So on-site IT is not necessarily the solution, unless it is done to certain standards. In all honesty, most installations probably do not meet those at the moment. And the cost associated with doing it properly may be considered excessive for your situation.
So it’s not as simple and not a black and white decision between “all on-site self-run” and “all in public cloud by US business”. There is a whole range of options in between that provide different advantages, disadvantages, costs and risks.
Weighing the risks
So whatever you do: There is always a risk analysis involved.
All businesses take risks based on educated guesses and sometimes even instinct. And they need to weigh cost against benefit. The perfect solution is rarely obtained, typically because it is excessively costly, so often businesses stick with “what works.” And their IT is no different in that regard.
It is a valid decision to say you’re not concerned about business secrets leaking, or consider the likely damage smaller than the risk of running a poorly secured IT under your own control either directly or through a third party. And the additional cost of running that kind of installation well does not seem justified in comparison to what you gain. So you go to a more trustworthy local provider that runs your installation on Open Source and Open Standards. Or you use the services of a large US public cloud vendor. It’s your call to make.
But I would argue this call should always be made consciously, in full knowledge of all risks and implications. And truth is that in too many cases people did not take this into account, it was more convenient to ignore and dismiss as unproven speculation . Only that it’s only speculation as long as it hasn’t been proven. So virtually any business right now should be re-evaluating its IT strategy to see what risks and benefits are associated with their current strategy, and whether another strategy might provide a more adequate approach.
And when that evaluation is done, I would suggest to look at the Total Cost of Operations (TCO). But not in an overly simplistic way, because most often the calculation is skewed in favour of proprietary lock-in. So always make sure to factor in cost of decommissioning the solution you are about to introduce. And the TCO isn’t everything.
IT is not just a cost, there is a benefit. All too often two alternatives are compared purely on the grounds of their cost. So more often than not the slightly cheaper solution will be chosen despite offering dramatically fewer benefits and a poor strategic outlook. And a year later you find out that it actually wasn’t cheaper, at all, because of hidden costs. And that you would have needed the benefits of the other solution. And that you’re in a strategic dead-end.
So I would always advocate to also take into account the benefits, both in things you require right now, and in things that you might be able to achieve in the future. For lack of a common terminology, let’s call this the Option Value Generated (OVG) for your business, both in gained productivity, as well as innovative potential. And then there is what I now conveniently name the Customer Confidence Impact (CCI) of both your ability to devise an efficient IT strategy, as well as how you handle their business, data and trust.
After all is said and done, you might still want to run US technology. And you might still want to use a public cloud service. If you do, be transparent about it, so your customers can choose whether or not they agree to that usage by being in business with you. Because some people are likely to take offence due to the social implications and ownership of their own data. In other words: Make sure those who communicate with you and use your services know where that data ends up.
This may not be a problem for your business and your customers. They may consider this entirely acceptable, and that is fine. Being able to make that call is part of what it means to have freedom to try out business approaches and strategies.
But if you do not communicate your usage of this service, be aware of the risks you might be incurring. The potential impact for customer confidence and public image for having misled your business associates and customers is dramatic. Just look at the level of coverage PRISM is getting and you’ll get an idea.
The door is wide open
When reviewing your strategy, keep in mind that you may require some level of ability to adapt to a changed world in the future. Nothing guarantees that better than Open Source and Open Standards. So if you have ignored this debate throughout the past years, now would be the time to take a look at the strategic reasons for the adoption of Free Software. Most importantly transparency, security, control, ability to innovate.
While the past ten years most of the debate has been around how Open Source can provide more efficient IT at better price for many people, PRISM has demonstrated that the strategic values of Free Software were spot on and are providing benefits for professional use of IT that proprietary software cannot hope to match.
Simultaneously the past 20 years have seen a dramatic growth of professional services in the area. Because benefits are nice in theory, but if they cannot be made use of because the support network is missing, they won’t reach the average business.
In fact, in the spirit of full disclosure, I speak of personal experience in this regard. Since 2009 I dedicated myself to building up such a business: Kolab Systems is an Open Source ISV for the Kolab Groupware Solution. We built this company because Kolab had a typical Open Source problem. Excellent concepts and technology, but a gap in professional support in services to allow wide adoption and use of that technology. That’s been fixed. We now provide support for on-site hosting as well as Kolab as a service through MyKolab.com. We even structured our corporate group to be able to take care of high security requirements in a verifiable way.
But we are of course not the only business that has built its business around combining the advantages of software freedom with professional services for its customers. There are so many businesses working on this that it would be impossible to list them all. And they provide services for customers of all sizes – up to the very largest businesses and governments of this world.
So the concerns are real, as are the advantages. And there is a plethora of professional services at your disposal to make use of the advantages and address the concerns.
The only question is whether you will make use of them.
All articles:







SFD Call to Action: Let the STEED run!
Information Technology is a hype driven industry, a fact that has largely contributed to the current situation where the NSA and GCHQ have unprecedented access to the global communication and information. Including for a very Realpolitik based approach to how that information may be used. Economic and political manipulation may not be how these measures are advertised, but it may very well be the actual motivation. It’s the economy, stupid!
Ever since all of this started, many people have asked the question how to protect their privacy. Despite some there is still a lack of comprehensive answers to this question. There is an obvious answer that most mainstream media seem to have largely missed: Software freedom advocates had it right all along. You cannot trust proprietary cryptography, or proprietary software. If a company has a connection to the legal nexus of the United States, it is subject to US law and must comply with demands of the NSA and other authorities. But if that company also provides proprietary software it is virtually impossible for you to know what kind of agreements it has with the NSA, as most of their management prefer not to go to jail. But one would have to be very naive to think the United States is the only country where secret agreements exist.
Security unfortunately is a realm full of quacks and it is just as easy to be fooled as it is to fool yourself. In fact many of the discussions I’ve had over the past weeks painfully reminded me of what Cory Doctorow called “Schneier’s Law” although Bruce Schneier himself points out the principle has been around for much longer. He has dated it back to Charles Babbage in 1864:
So in my experience it makes good sense to listen to what Bruce Schneier and a few others have to say, which is why I think his guide to staying secure on the internet is probably something everyone should have read. In that list of recommendations there are some points that ought to read familiar:
“So you were right, good for you” I hear you think. The point I am trying to make is a different one. It has been unbelievably difficult in the past to consequently do the right thing that would now give us the answers to the questions posed by the NSA and others. Both the Free Software Foundation Europe (FSFE) as an organisation and Kolab as a technology have a very long history to that extent. In fact if you’ve read the background of MyKolab.com, you’ll hopefully see the same kind of approach there, as well. Having been involved with both has given me a unique perspective.
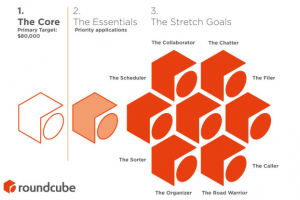
And we will continue to do that, both through MyKolab.com and some other development projects we are pushing with Kolab Systems for customers that have an interest in these technologies. But they have a whole lot more in mind than we could make possible immediately, such as dramatically increasing the usability for end-to-end cryptography. The concept they have developed is based on over a decade of working on obstacles to end user adoption. It’s called STEED — Usable End-to-End Encryption and has been available for two years now. I think it’s time to be finalized and implemented.
That’s why I am using tomorrow’s Software Freedom Day to ask for volunteers to help them run a crowdfunding campaign so they can finally put it into practice, in the open, to everyone’s benefit. Because that’s going to contribute more than just a little bit towards a world where privacy will once more be the default. So please help spread the word and let the STEED run!