After a somewhat brief overview over the world we find ourselves in, the question is what does this mean to us as a society?
As highlighted in the previous article, governments have no realistic option not to engage in some form of activities to protect their people from threats that originate on-line or have an on-line component. These were the grounds for German chancellor Angela Merkel to make statements of support for PRISM. The problem is that I doubt it is effective and adequate to the threat. The side effects seem out of sync with the gain. That this gain is only claimed, not proven due to alleged security concerns, also does nothing to help the case.
It has become public knowledge these technologies exist and make mass surveillance can and is being implemented, and works efficiently. Calling for a general ban is unrealistic, and naive. Of course these technologies will be used against people, businesses and governments by someone – be they states or organisations. So the actual question is: Which are the circumstances under which use of such technology is acceptable?
Looking at the initial reactions, a great number of people – consciously or not – base their reaction on Article 12 of the Universal Declaration of Human Rights. And considering the consequences, that does not seem very far fetched.
Consequences of the Surveillance Society
There are some stories floating around where people have suffered repercussions such as being denied entry to the United States. But that’s probably the extent of it for many of us unless you are a public figure, or ever find yourself in a job where you would have influence on a decision that might be of major consequence to the United States.
But that’s only the fairly superficial perspective.
Consider for a moment the Arab spring where governments desperately tried to remain in power. In several cases the governments overthrown were the same ones that received strategic and practical support by the United States – including military and secret service activities – as part of their plans for the region. These governments in their desperate attempts to retain control knew which activists to imprison, sometimes torture and often confronted them with their own private messages from Facebook and Twitter.
Could those governments have to obtained that data itself? Possibly. But there is another option.
FISA makes it legal for the United States to obtain and make use of that data for the strategic interests of the United States. And Prism would have made it almost trivial. So the simpler way for those governments to know what was planned would have been to receive dossiers from their US contacts. Does this prove it happened that way? Certainly not. But it demonstrates the level of influence this combination of technical ability is giving the United States and other countries.
“Still,” most people think ‘I am living in a safe country and have no plans to overthrow my government.’
“Nothing to hide, nothing to fear” has been used to justify surveillance for a long time. It’s a simple and wrong answer. Because everyone has areas they would prefer to remain private. If someone has the ability to threaten you with exposing something you do not wish to see exposed, they have power over you. But what’s more: People who have to assume to be watched at all times, even in their most intimate moments and inner thoughts, behave differently.
A culture of surveillance leads to self regulation, with fundamental impact how people behave at all times. Will you still speak up against things you perceive as wrong when you fear there might be repercussions? Or would you perhaps ask yourself whether this particular issue is important enough to risk so much, and hope that it won’t be as bad, or that someone else will take action?
Also, consider the situation of people who absolutely rely upon a certain level of privacy for their professional lives, such as lawyers, journalists and others. That no-one in these professions should be using these services should be self-evident. But if a society adopts the “Nothing to hide, nothing to fear” dogma, those who communicate for good reason with such professions will stand out as dark shadows in an otherwise fully lit room, and will raise suspicion.
If privacy becomes the exception those who require privacy will easily be singled out. The only way to avoid this is to make privacy the norm: If everyone has privacy, no-one will be suspicious for it.
And there are good reasons you would want to do your part to live in such a society, because the functioning of democracy as a whole is linked to a set of factors, including a working media, ability to form political opinion, and become politically active to achieve change for the better. And even if you yourself have no ambition in this way at this point in time.
Privacy is one of the essential building blocks of a free society.
You might find yourself activated by misspent tax money, a new highway being planned through your back yard, or the plans to re-purpose your favourite city park for a shopping mall. And if it isn’t yourself, perhaps something will make your parents, siblings, spouse, kids, best friend want to take action and then require a society that grants privacy in order not to be intimidated into silence.
So there are good reasons why people worry about this level of surveillance.
Why, then, are they choosing to voluntarily support it?
Feudal Agents of the Totalitarian State
It has been subject of discussion in the software freedom community for some time, but only now appears to hit the radar of a larger subset of the forward thinking IT literates: The large US service providers own users and their data in ways that led security guru Bruce Schneier to comparing them to feudal lords, leaving their users as hapless peasants in a global Game of Thrones power struggle.
Some time ago already, Geek & Poke probably summarized it slightly more pointedly:
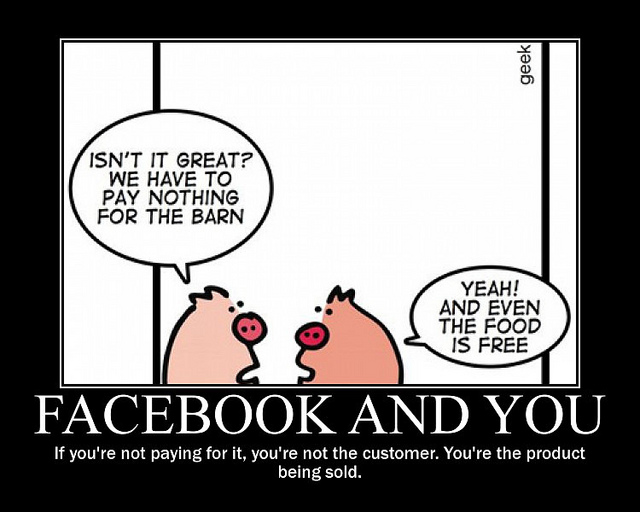
One aspect of using these services is that users place themselves under surveillance as part of their payment for the service. The plethora of knowledge Facebook keeps on everyone that is using it, and everyone that is not using it, has been disclosed time and again, last time during the shadow profile exposure. But this has not been the first time. Nor can anyone reasonably expect Google, Microsoft or Apple to behave any different.
What is important to understand is that the centralisation of these services, and turning devices into increasingly dumb data gathering and supply devices is not accidental, nor is it technologically necessary. We all carry around a lot more computing power all the time than was readily available just some years ago.
So these devices and services could operate in a de-centralized and meshed fashion.
But then the companies would not get to profile their users in such detail, potentially gathering every intimate detail about them, such as whether they were aroused when they last used voice search to find the nearest hotel. Or did you think that command was analysed on your smart phone, and not by the (almost) infinitely powerful processing power in the data centres of your service provider?
Data is the new gold, and these companies are mining it as best they can.
Naturally these companies are always downplaying the amount of data collected, or the impact that use of this data might have on individuals. PRISM exposed this carefully crafted fallacy to some extent.
It also raised the question: What is it worse? That the government which can be held accountable to a larger degree gets access to some data gathered by a company? Or that a company that is responsible to no-one but its shareholders gathered all of it?
In fact, cynically speaking, one might even think these companies are mostly unhappy about the fact that the US government wants free, unlimited access to the raw data rather than the paid for refined access they offer as part of their business model.
But the root cause is in the centralised gathering of such data under terms that do not make these companies your service providers, but you their peasant. This treasure trove will always attract desires, and countries have ways to get access because they have ways to impact profits. Now that the PRISM disclosure taught them what’s possible, countries such as Turkey are quickly catching on, demanding access to details of Gezi protesters.
So while these companies are often wrapping themselves in liberty, the internet and all that is good for humankind, by their existence and business model they make a contribution to a totalitarian society.
Whether that contribution is decisive, or outweighs the instances where they do good, I cannot judge.
But using these providers for your services and getting all up in arms about PRISM is somewhat hypocritical, I’m afraid. It’s a bit like complaining about losing your foot when you’ve voluntarily and without need amputated your entire leg before to be able to make use of the special “one-legged all you can eat buffet.”
Choices for Free Citizens
So assuming you want to break free of this surveillance and the tendencies towards a totalitarian society, which are your options?
Firstly, choose Open Source / Free Software and Open Standards. There is a plethora of applications out there and the way in which their internal workings and control structures are transparent and publicly developed makes it much more likely they will not provide back doors to your data. Following the PRISM leaks, sites such as http://prism-break.org have sprung up that try to help you do just that.
Secondly, start making use of encryption, which is easier and more effective than you might think.
Chances are that someone in your circle of friends or family is already using some or even many of these applications. Get them to help you get started yourself.
But assuming you are not a technical person, which is most of society, the most important choice you can likely make is with your feet and wallet by choosing services that work for you and put themselves at your service – rather than services that process you and put you at their service.
The important place for this is to look at the terms of the services you are using.
I know this is tedious, and these terms are often deliberately written to make eyes glaze over when trying to understand what they actually say.
But there is a web site that can help you with it: Terms of Service; Didn’t Read. Check out the services you are currently using, and get yourself the browser extension so you at least start getting an idea of what kinds of rights you are surrendering by making use of the services.
As for providers that offer you the same convenience, but without the mandatory cavity search, there are still quite a few. Naturally it makes sense to look at their terms of services carefully, ensure they are based in a legislation of your choice, and use technologies that you can trust. If you are not sure, ask them to explain what standards they observe with regards your data. And ensure you can switch providers, even switch to self-hosting if you want to, without necessarily changing technologies.
And once you’ve looked through all those criteria and made your homework on which solutions can deliver all of this, without compromise, take control of your data and software.
Disclaimer
I’m not a party without interest in this debate. You can easily inform yourself about what I’ve done in the past in this area. And my past years I’ve dedicated to building a technology that would allow people to own their data and software, while providing all the features users have grown accustomed to.
That technology is called Kolab, and of course I’d be delighted if you got in touch with us, or installed Kolab.org on your own, or even made use of the http://MyKolab.com service. Because all of this will help us continue to work to the goal of allowing people secure, powerful collaboration across platforms while owning their own data and software.
But it’s this work that has followed from my analysis, not the other way around.
So make up your own mind.
All articles:

The Post-PRISM Society: Totalitarian Clouds
After a somewhat brief overview over the world we find ourselves in, the question is what does this mean to us as a society?
As highlighted in the previous article, governments have no realistic option not to engage in some form of activities to protect their people from threats that originate on-line or have an on-line component. These were the grounds for German chancellor Angela Merkel to make statements of support for PRISM. The problem is that I doubt it is effective and adequate to the threat. The side effects seem out of sync with the gain. That this gain is only claimed, not proven due to alleged security concerns, also does nothing to help the case.
It has become public knowledge these technologies exist and make mass surveillance can and is being implemented, and works efficiently. Calling for a general ban is unrealistic, and naive. Of course these technologies will be used against people, businesses and governments by someone – be they states or organisations. So the actual question is: Which are the circumstances under which use of such technology is acceptable?
Looking at the initial reactions, a great number of people – consciously or not – base their reaction on Article 12 of the Universal Declaration of Human Rights. And considering the consequences, that does not seem very far fetched.
Consequences of the Surveillance Society
There are some stories floating around where people have suffered repercussions such as being denied entry to the United States. But that’s probably the extent of it for many of us unless you are a public figure, or ever find yourself in a job where you would have influence on a decision that might be of major consequence to the United States.
But that’s only the fairly superficial perspective.
Consider for a moment the Arab spring where governments desperately tried to remain in power. In several cases the governments overthrown were the same ones that received strategic and practical support by the United States – including military and secret service activities – as part of their plans for the region. These governments in their desperate attempts to retain control knew which activists to imprison, sometimes torture and often confronted them with their own private messages from Facebook and Twitter.
Could those governments have to obtained that data itself? Possibly. But there is another option.
FISA makes it legal for the United States to obtain and make use of that data for the strategic interests of the United States. And Prism would have made it almost trivial. So the simpler way for those governments to know what was planned would have been to receive dossiers from their US contacts. Does this prove it happened that way? Certainly not. But it demonstrates the level of influence this combination of technical ability is giving the United States and other countries.
“Still,” most people think ‘I am living in a safe country and have no plans to overthrow my government.’
“Nothing to hide, nothing to fear” has been used to justify surveillance for a long time. It’s a simple and wrong answer. Because everyone has areas they would prefer to remain private. If someone has the ability to threaten you with exposing something you do not wish to see exposed, they have power over you. But what’s more: People who have to assume to be watched at all times, even in their most intimate moments and inner thoughts, behave differently.
A culture of surveillance leads to self regulation, with fundamental impact how people behave at all times. Will you still speak up against things you perceive as wrong when you fear there might be repercussions? Or would you perhaps ask yourself whether this particular issue is important enough to risk so much, and hope that it won’t be as bad, or that someone else will take action?
Also, consider the situation of people who absolutely rely upon a certain level of privacy for their professional lives, such as lawyers, journalists and others. That no-one in these professions should be using these services should be self-evident. But if a society adopts the “Nothing to hide, nothing to fear” dogma, those who communicate for good reason with such professions will stand out as dark shadows in an otherwise fully lit room, and will raise suspicion.
If privacy becomes the exception those who require privacy will easily be singled out. The only way to avoid this is to make privacy the norm: If everyone has privacy, no-one will be suspicious for it.
And there are good reasons you would want to do your part to live in such a society, because the functioning of democracy as a whole is linked to a set of factors, including a working media, ability to form political opinion, and become politically active to achieve change for the better. And even if you yourself have no ambition in this way at this point in time.
Privacy is one of the essential building blocks of a free society.
You might find yourself activated by misspent tax money, a new highway being planned through your back yard, or the plans to re-purpose your favourite city park for a shopping mall. And if it isn’t yourself, perhaps something will make your parents, siblings, spouse, kids, best friend want to take action and then require a society that grants privacy in order not to be intimidated into silence.
So there are good reasons why people worry about this level of surveillance.
Why, then, are they choosing to voluntarily support it?
Feudal Agents of the Totalitarian State
It has been subject of discussion in the software freedom community for some time, but only now appears to hit the radar of a larger subset of the forward thinking IT literates: The large US service providers own users and their data in ways that led security guru Bruce Schneier to comparing them to feudal lords, leaving their users as hapless peasants in a global Game of Thrones power struggle.
Some time ago already, Geek & Poke probably summarized it slightly more pointedly:
One aspect of using these services is that users place themselves under surveillance as part of their payment for the service. The plethora of knowledge Facebook keeps on everyone that is using it, and everyone that is not using it, has been disclosed time and again, last time during the shadow profile exposure. But this has not been the first time. Nor can anyone reasonably expect Google, Microsoft or Apple to behave any different.
What is important to understand is that the centralisation of these services, and turning devices into increasingly dumb data gathering and supply devices is not accidental, nor is it technologically necessary. We all carry around a lot more computing power all the time than was readily available just some years ago.
So these devices and services could operate in a de-centralized and meshed fashion.
But then the companies would not get to profile their users in such detail, potentially gathering every intimate detail about them, such as whether they were aroused when they last used voice search to find the nearest hotel. Or did you think that command was analysed on your smart phone, and not by the (almost) infinitely powerful processing power in the data centres of your service provider?
Data is the new gold, and these companies are mining it as best they can.
Naturally these companies are always downplaying the amount of data collected, or the impact that use of this data might have on individuals. PRISM exposed this carefully crafted fallacy to some extent.
It also raised the question: What is it worse? That the government which can be held accountable to a larger degree gets access to some data gathered by a company? Or that a company that is responsible to no-one but its shareholders gathered all of it?
In fact, cynically speaking, one might even think these companies are mostly unhappy about the fact that the US government wants free, unlimited access to the raw data rather than the paid for refined access they offer as part of their business model.
But the root cause is in the centralised gathering of such data under terms that do not make these companies your service providers, but you their peasant. This treasure trove will always attract desires, and countries have ways to get access because they have ways to impact profits. Now that the PRISM disclosure taught them what’s possible, countries such as Turkey are quickly catching on, demanding access to details of Gezi protesters.
So while these companies are often wrapping themselves in liberty, the internet and all that is good for humankind, by their existence and business model they make a contribution to a totalitarian society.
Whether that contribution is decisive, or outweighs the instances where they do good, I cannot judge.
But using these providers for your services and getting all up in arms about PRISM is somewhat hypocritical, I’m afraid. It’s a bit like complaining about losing your foot when you’ve voluntarily and without need amputated your entire leg before to be able to make use of the special “one-legged all you can eat buffet.”
Choices for Free Citizens
So assuming you want to break free of this surveillance and the tendencies towards a totalitarian society, which are your options?
Firstly, choose Open Source / Free Software and Open Standards. There is a plethora of applications out there and the way in which their internal workings and control structures are transparent and publicly developed makes it much more likely they will not provide back doors to your data. Following the PRISM leaks, sites such as http://prism-break.org have sprung up that try to help you do just that.
Secondly, start making use of encryption, which is easier and more effective than you might think.
Chances are that someone in your circle of friends or family is already using some or even many of these applications. Get them to help you get started yourself.
But assuming you are not a technical person, which is most of society, the most important choice you can likely make is with your feet and wallet by choosing services that work for you and put themselves at your service – rather than services that process you and put you at their service.
The important place for this is to look at the terms of the services you are using.
I know this is tedious, and these terms are often deliberately written to make eyes glaze over when trying to understand what they actually say.
But there is a web site that can help you with it: Terms of Service; Didn’t Read. Check out the services you are currently using, and get yourself the browser extension so you at least start getting an idea of what kinds of rights you are surrendering by making use of the services.
As for providers that offer you the same convenience, but without the mandatory cavity search, there are still quite a few. Naturally it makes sense to look at their terms of services carefully, ensure they are based in a legislation of your choice, and use technologies that you can trust. If you are not sure, ask them to explain what standards they observe with regards your data. And ensure you can switch providers, even switch to self-hosting if you want to, without necessarily changing technologies.
And once you’ve looked through all those criteria and made your homework on which solutions can deliver all of this, without compromise, take control of your data and software.
Disclaimer
I’m not a party without interest in this debate. You can easily inform yourself about what I’ve done in the past in this area. And my past years I’ve dedicated to building a technology that would allow people to own their data and software, while providing all the features users have grown accustomed to.
That technology is called Kolab, and of course I’d be delighted if you got in touch with us, or installed Kolab.org on your own, or even made use of the http://MyKolab.com service. Because all of this will help us continue to work to the goal of allowing people secure, powerful collaboration across platforms while owning their own data and software.
But it’s this work that has followed from my analysis, not the other way around.
So make up your own mind.
All articles:
About Georg Greve
Georg Greve is a technologist and entrepreneur. Background as a software developer and physicist. Head of product development and Chairman at Vereign AG. Founding president of the Free Software Foundation Europe (FSFE). Previously president and CEO at Kolab Systems AG, a Swiss Open Source ISV. In 2009 Georg was awarded the Federal Cross of Merit on Ribbon by the Federal Republic of Germany for his contributions to Open Source and Open Standards.